With recent high profile hacks, like what happened with Code Spaces and the @n twitter hack, simply using passwords is becoming something that is inadequate as attackers are becoming more and more complex in their techniques.
An attacker getting access to your password can cripple your business or erase your online identity.
With that in mind, if you are building a cloud application, maybe you're building the next big CRM software as a service; you owe it to your end users to provide them with the highest security possible.
What is Multi-factor Authentication?
I'm glad you asked, Multi-factor Authentication, or MFA for short, is a technique to provide more security during signing-in, while still maintaining a simple sign-in procedure. Simply put, it requires using more than one verification method to verify that you are, you.
It works by requiring any two or more of the following verification methods:
- Something you know (typically a password)
- Something you have (a trusted device that is not easily duplicated, like a phone)
- Something you are (biometrics)
MFA and Azure
Depending on how you built your application, you have several options for adding MFA functionality.
In this post, I'll assume you're not using Azure Active Directory, and that you have your own implementation of a users database that you want to protect with MFA, hence I'll be implementing MFA using the MFA SDK. The Multi-Factor Authentication SDK is available for C#, Visual Basic (.NET), Java, Perl, PHP, and Ruby.
Show me the money
Creating the project
I'll start by creating a new ASP.net MVC website 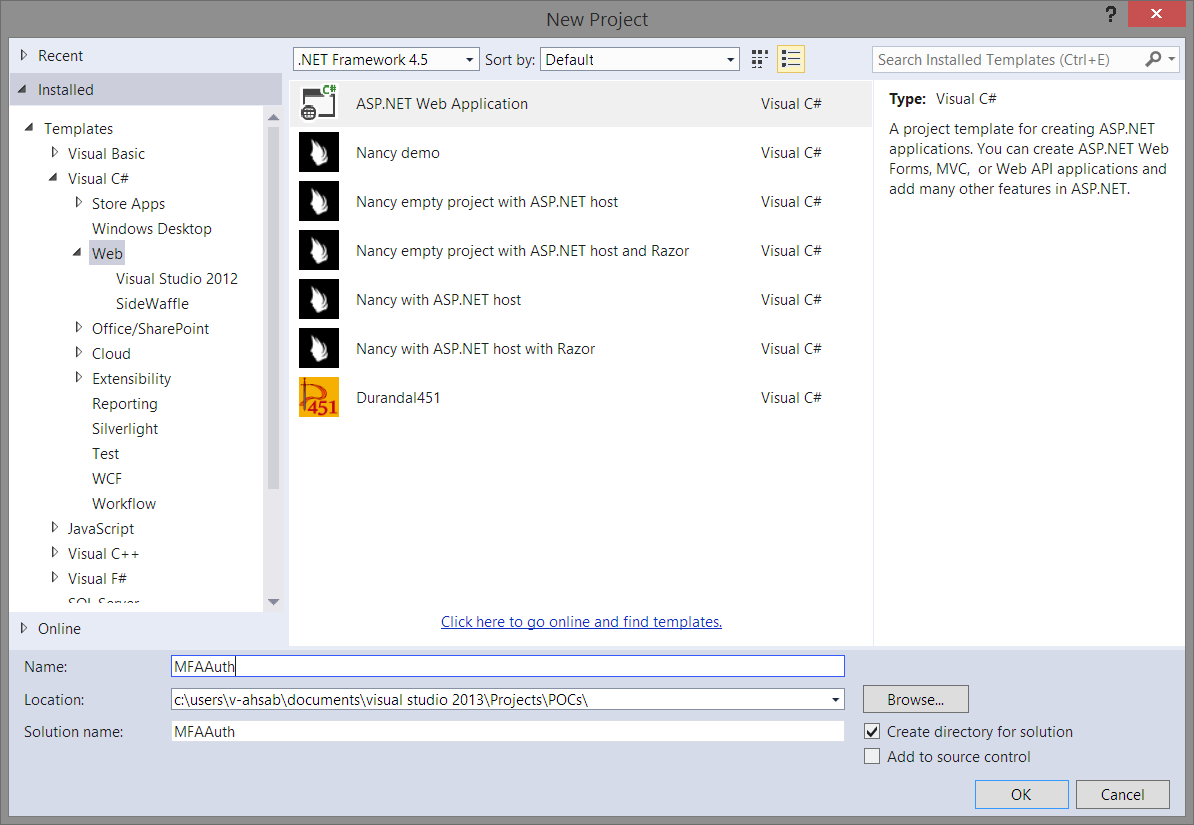
Essentially, this will create the required plumbing ie: Account controller, database tables, views, etc. that are needed for quickly spinning up a login form. You could opt not to use the ASP.NET identity if you want and integrate your own database, but I highly recommend you take a look at it. It is awesome!
Adding fields for the phone number and PIN in the Model and database
Migrations are recommended to use when you are modifying the schema of the database or you are changing the Code First Model. ASP.NET Identity uses Entity Framework Code First as an underlying framework. For more information on EF migrations please visit http://msdn.microsoft.com/en-us/data/jj591621
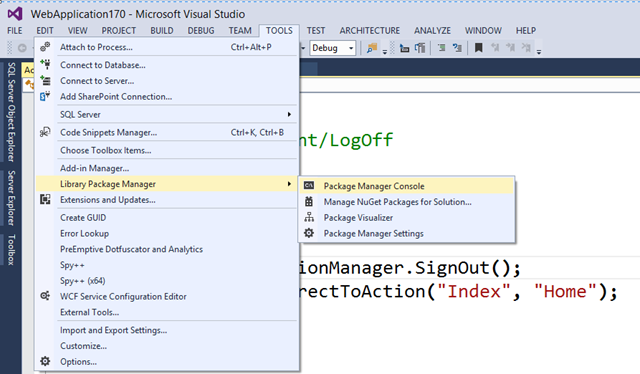
Bring up the Package Manager Console then go ahead and enable-migrations.
After migrations are enabled, open Models\IdentityModels.cs and add Country Code, Phone and PIN properties to the ApplicationUser class.
Now in the Package Manager Console, run add-migration adding_mfa_fields
Finally run update-database to apply the changes to the database.
Adding the fields during registration
Now let's update our RegisterViewModel in Models\AccountViewModels.cs to add the same fields, so that we're able to access them during registration.
Then update the Register method in the AccountController.cs to pass on the additional fields to the ApplicationUser
Finally, let's add the fields in Views\Register.cshtml
Run and register a new user
Create a Multi-factor Authentication Provider on Azure
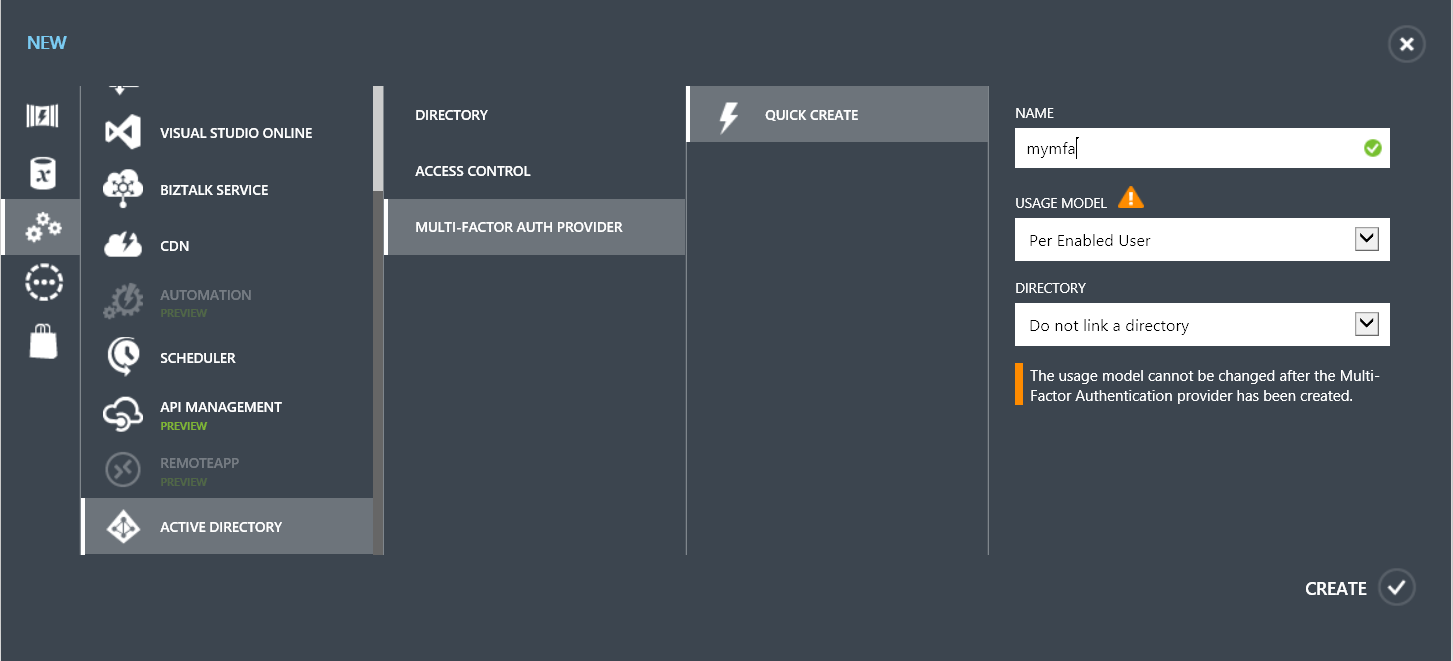
On the portal click on the big New button, then create a new Multi-factor Auth provider. Do not link it to a directory, and make sure you select the appropriate usage model because you can't change it later.
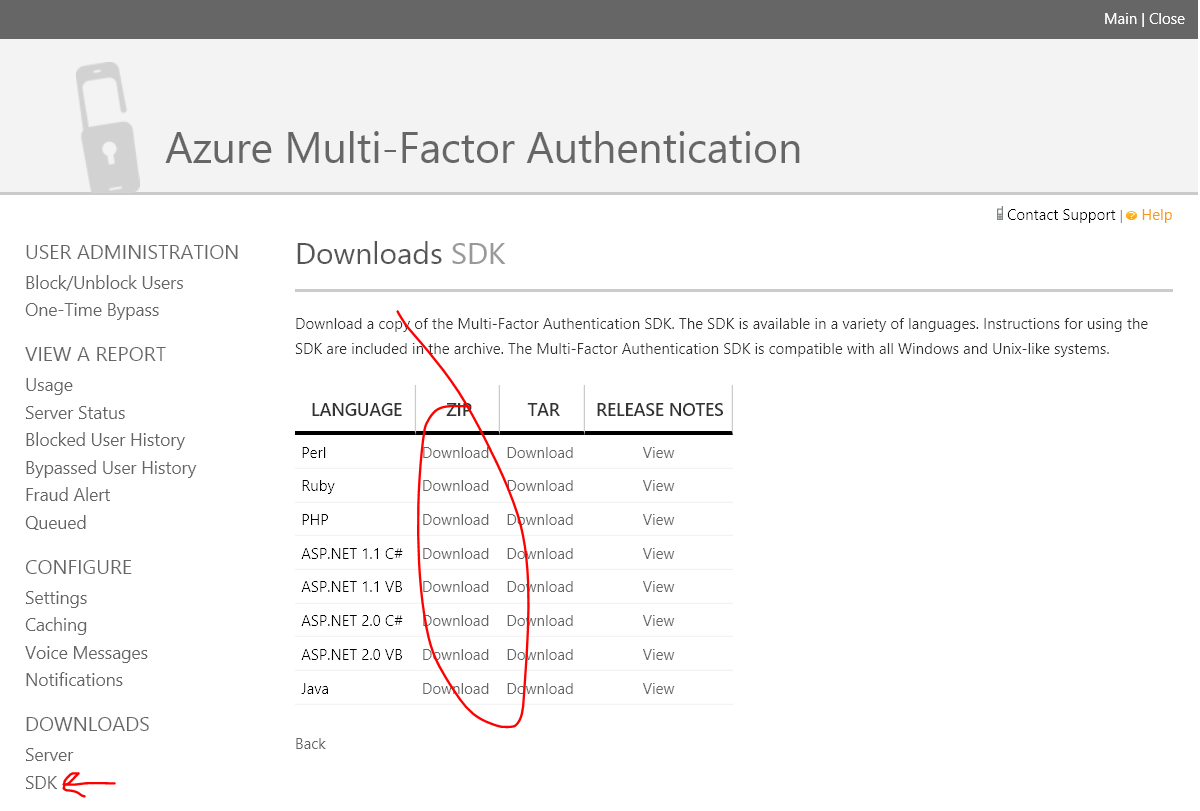
Download the SDK
Once your provider is provisioned, you need to click on Manage to open its management portal and download the appropriate SDK.
Download the ASP.NET 2.0 C# SDK and extract it somewhere.
Add the SDK to the project
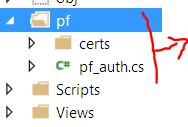
Open the extracted zip file, and copy the pf folder into your project, then add the files to the project.
Modify the Login
Modify the Login method in AccountController.cs to include calls to the MFA provider. Note that in the code below, there are some commented options. Basically, these are different ways you can initiate the authentication varying between a phone call, SMS and voice prints.
Test it!
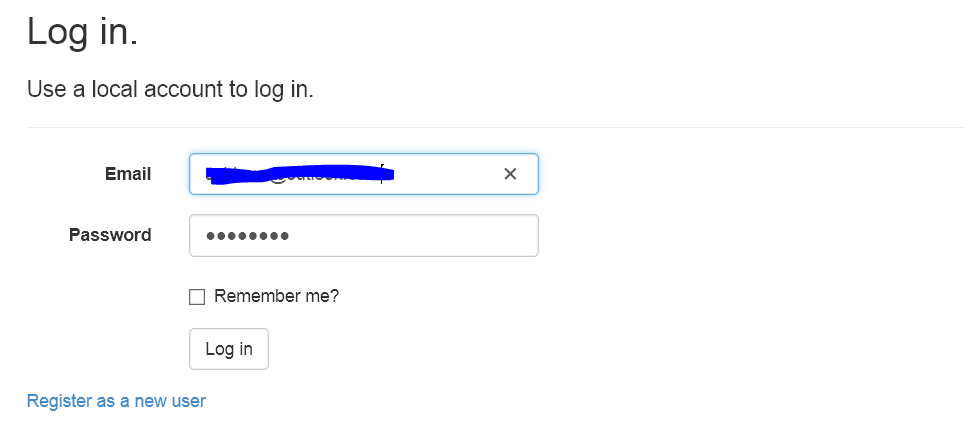
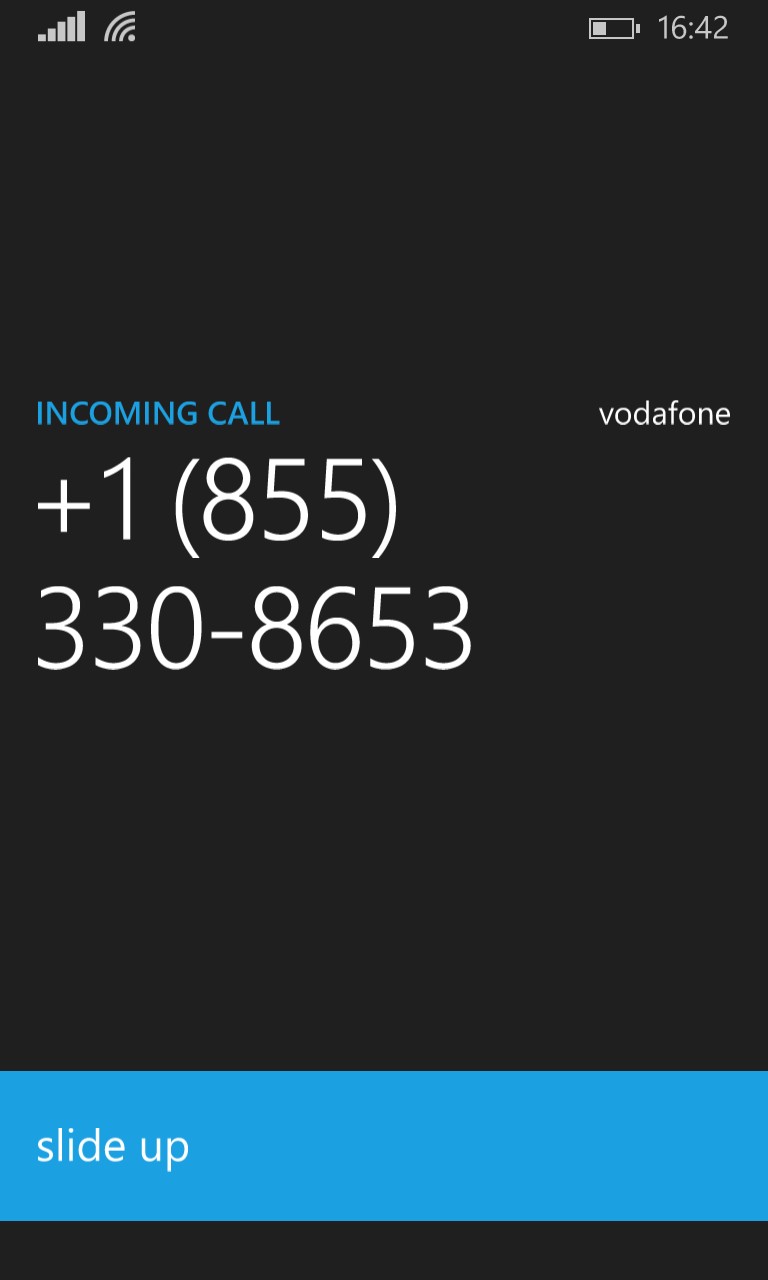
Run the site and click on Log In then enter your username and password, you should be getting a phone call that you have to accept in order to be logged in.
You will get a phone call (or SMS) that you have to pick up
Closing
We've implemented Multi-factor Authentication in a pretty straight forward way and added a strong layer of security. If you want to try this out, you can go ahead and create a 30-day free trial for Azure.